

David Santefort (physics major, math minor), Matthew Bunda (physics major, math minor), Joe Onesto (math and computer science double major), and Matthew Knight (math major) were inducted into the Illinois Iota Chapter of Pi Mu Epsilon (PME), the national Math Honors Society, on Thursday, October 27th, as part of the ACCA Math Lecture Series.

Congratulations to these four brilliant mathematicians on becoming the newest members of PME.
October is National Cyber Security Awareness Month (NCASM). NCASM is a time set aside by the Department of Homeland Security (DHS) to help raise awareness of the growing and persistent threat posed by cyber breaches against individuals, organizations, and critical infrastructures. Dr. Ray Klump, Chair of Computer and Mathematical Sciences, kicked off Lewis University's recognition of NCASM with an Arts and Ideas talk.
Each week of NCSAM focuses on a particular theme. The first week promotes cyber security as a personal and shared responsibility through a campaign called "Stop. Think. Connect." DHS provides a number of valuable tools and tips on its website to educate citizens about the pitfalls they face online and to prepare them to steer around them. The site includes links to advice for keeping your cell phone secure and for using social media privately and responsibly. The site also includes tips for what to do if an when you become the victim of cyber crime.
The second week promotes the theme "Cyber from the break room to the board room." Organizations must promote a pervasive sense of vigilence against cyber threats. An organization's members must take personal responsibility for their actions online and their role in keeping the organization's data secure. Likewise, an organization's leaders must prioritize cyber security as a top concern and dedicate their efforts and resources accordingly. Preventing cyber attack can't be a top-down effort. It requires widespread commitment. That includes avoiding clicking unthinkingly on links in emails and documents, using encryption consistently and ubiquitously, and employing multifactor authentication instead of just passwords whenever possible.
Week 3 of NCSAM addresses cyber crime and what to do if you fall victim to it. The average cyber security heist costs an organization over $670,000. Costs practically double when health care records are stolen. Most victims are small and medium-sized businesses, and the majority of those that are attacked close within 6 months of the breach. The consequences of a cyber attack are dire to organizations and individuals alike. If you fall prey to a cyber attack, you should contact law enforcement immediately, and you should report the incident to www.ic3.gov.
In Week 4, NCSAM addresses how to balance our ever-connected lives with the need to exercise caution online. Mobile apps make going online amazingly ease, but that ease can make us let down our guard. When we install a new app on our phones, do we trust it? What kinds of permissions do we grant that app? And we can't talk just about our cell phones. All those devices we use in our homes and businesses, including smart thermostats and video game machines and products that respond to voice commands, store and communicate our information. This "internet of things" also poses a significant danger that is expected to grow as the number of connected devices soars to 40 billion over the next 5 years. Just because a device doesn't look like a computer doesn't mean it's immune to cyber attack. Again, responsible usage, which includes caution when sharing data through them and making sure that we install patches to fix their security problems, is an absolute requirement if we are going to remain safe.
Unfortunately, that leaves just one day - Halloween - to focus on what is probably the scariest reality of the cyber security threat: how susceptible our critical infrastructures are to attack. Critical infrastructures include the electric power grid, water filtration systems, gas pipelines, transportation, banking, logistics, and any other geographically expansive network that provides crucial products and services. These networks are increasingly computerized and automated. As a result, they are terribly susceptible to cyber attack. In fact, the first known successful attack against an electric power grid occurred in the Ukraine on December 23, 2015. The electrical grid in the United States is, arguably, just as susceptible. Researchers currently explore ways to keep these kinds of critical systems secure, but it is a daunting task.
National Cyber Security Awareness Month isn't exactly what one would call a cause for celebration. It serves as a sobering reminder that our increasingly digital lives come at a price and carry great risk. That doesn't mean that we somehow must abandon our devices. It simply means that we must be smarter, more cautious, more watchful, and more willing to work together to face down cyber threats.
Computer Science alumnus Tom Drez gave a talk on cyber security to Lewis students on September 21, 2016, at 7pm. The talk, entitled "Cyber Security, Cyber Risk, and Data Breaches, Oh My!" kicked off the ACCA Computer Science Seminar Series, which Lewis is hosting on the topic of cyber security this fall for the Associated Colleges of the Chicagoland Area (ACCA).
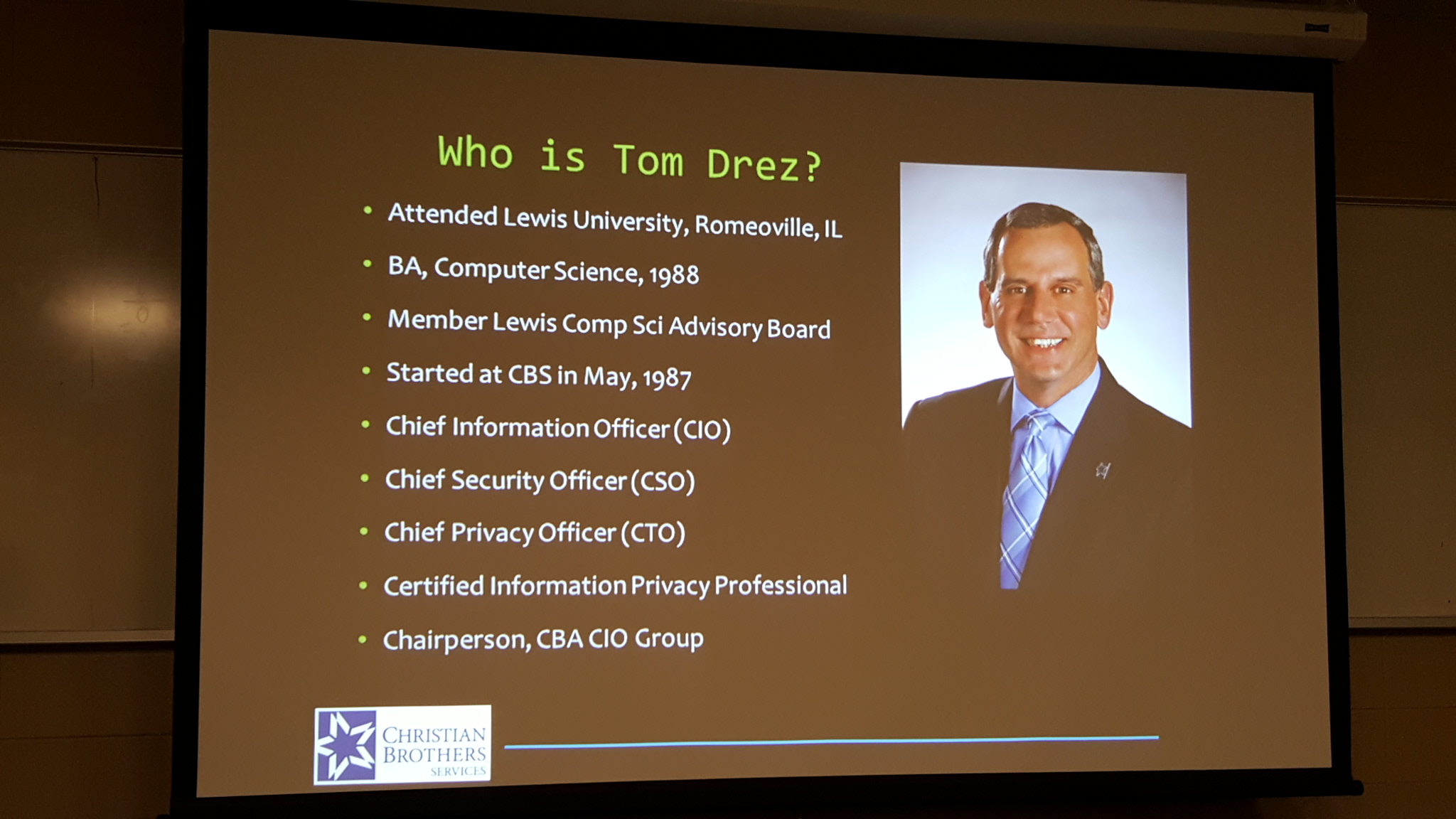
Tom focused on the significant threats facing today's organizations due to cyber security breaches. All sorts of data, including personally identifiable information, personal health information, non-publicly available financial information, and payment card industry information, is available to cyber thieves. And the losses caused by hackers have been profound. For example, 70 million customers were affected by the Target data breach in 2014. More recently, 80 million health insurance customers were impacted by a breach against Anthem that is suspected to have been perpetrated by Chinese hackers. The costs associated with these breaches are tremendous: the average cost of a breach is $674,000. In health care, the average cost of a data breach is twice that. The costs are alarming.
So, what can we do to defend ourselves? First, you have to realize that your organization's perimeter isn't your physical campus; it extends to wherever your employees are. So, you need to encrypt all sensitive data and try to keep it encrypted wherever it is transmitted and consumed. And you need to employ two-factor authentication so that hackers can't access systems just by knowing your username and password. They should also be forced to provide an on-the-spot code that only privileged users would be able to know. Finally, your organization's staff need to be kept constantly informed of the seriousness of the threats and how they are evolving. A knowledgeable workforce can go a long way toward strengthening your security posture.
CaMS is very grateful to Mr. Drez for taking the time to share his expertise with us.